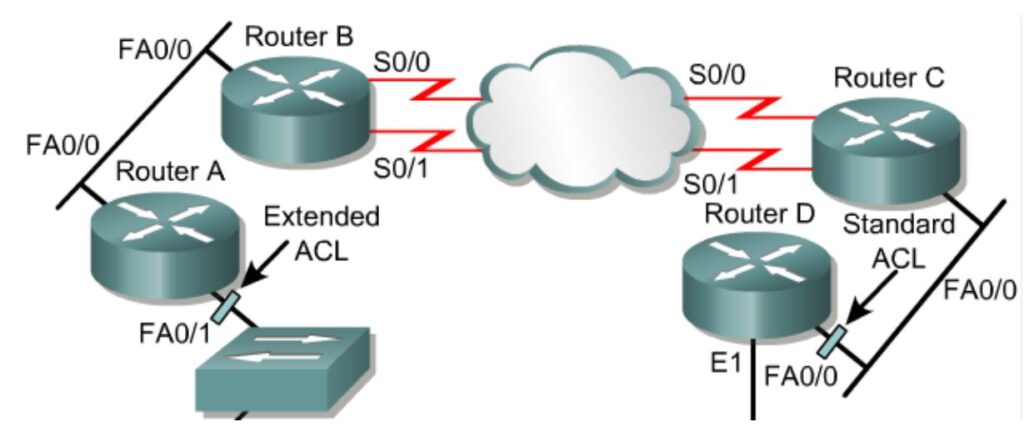
The general rule is to put the extended ACLs as close as possible to the source of the traffic denied. Standard ACLs do not specify destination addresses, so they should be placed as close to the destination as possible.
For example, in the graphic, a standard ACL should be placed on Fa0/0 of Router D to prevent traffic from Router A.
Permitting a Single Host:
Router(config)# access-list 1 permit 200.100.50.23 0.0.0.0 #or Router(config)# access-list 1 permit host 200.100.50.23 #or Router(config)# access-list 1 permit 200.100.50.23 (The implicit “deny any” ensures that everyone else is denied.) Router(config)# int e0 Router(config-if)# ip access-group 1 in #or Router(config-if)# ip access-group 1 out
Denying a Single Host:
Router(config)# access-list 1 deny 200.100.50.23 0.0.0.0 Router(config)# access-list 1 permit 0.0.0.0 255.255.255.255 or Router(config)# access-list 1 deny host 200.100.50.23 Router(config)# access-list 1 permit any (The implicit “deny any” is still present, but totally irrelevant.) Router(config)# int e0 Router(config-if)# ip access-group 1 in or Router(config-if)# ip access-group 1 out
Permitting a Single Network:
Class C Router(config)# access-list 1 permit 200.100.50.0 0.0.0.255 Class B Router(config)# access-list 1 permit 150.75.0.0 0.0.255.255 Class A Router(config)# access-list 1 permit 13.0.0.0 0.255.255.255 (The implicit “deny any” ensures that everyone else is denied.) Router(config)# int e0 Router(config-if)# ip access-group 1 in or Router(config-if)# ip access-group 1 out
Denying a Single Network:
Class C Router(config)# access-list 1 deny 200.100.50.0 0.0.0.255 Router(config)# access-list 1 permit any Class B Router(config)# access-list 1 deny 150.75.0.0 0.0.255.255 Router(config)# access-list 1 permit any Class A Router(config)# access-list 1 deny 13.0.0.0 0.255.255.255 Router(config)# access-list 1 permit any (The implicit “deny any” is still present, but totally irrelevant.)
Permitting a Class C Subnet:
Network Address/Subnet Mask: 200.100.50.0/28 Desired Subnet: 3rd Process: 32-28=4 2^4 = 16 1st Usable Subnet address range it 200.100.50.16-31 2nd Usable Subnet address range it 200.100.50.32-47 3rd Usable Subnet address range it 200.100.50.48-63 Subnet Mask is 255.255.255.240 Inverse Mask is 0.0.0.15 or subtract 200.100.50.48 from 200.100.50.63 to get 0.0.0.15 Router(config)# access-list 1 permit 200.100.50.48 0.0.0.15 (The implicit “deny any” ensures that everyone else is denied.)
Denying a Class C Subnet:
Network Address/Subnet Mask: 192.68.72.0/27 Undesired Subnet: 2nd Process: 32-27=5 2^5=32 1st Usable Subnet address range it 192.68.72.32-63 2nd Usable Subnet address range it 192.68.72.64-95 Subnet Mask is 255.255.255.224 Inverse Mask is 0.0.0.31 or subtract 192.68.72.64 from 192.68.72.95 to get 0.0.0.31 Router(config)# access-list 1 deny 192.68.72.64 0.0.0.31 Router(config)# access-list 1 permit any (The implicit “deny any” is still present, but totally irrelevant.)
Need expert help with this in production?
Youngster Company offers hands-on services for the topics covered on this blog — cybersecurity audits (ISO 27001 / IT compliance), penetration testing, DevOps automation, server & network configuration, and digital forensics / OSINT investigations. If you need this implemented, audited, or troubleshot for your business, get in touch.

Pingback: ACLs: Permit/Deny Source & Destination Addresses, and Protocols