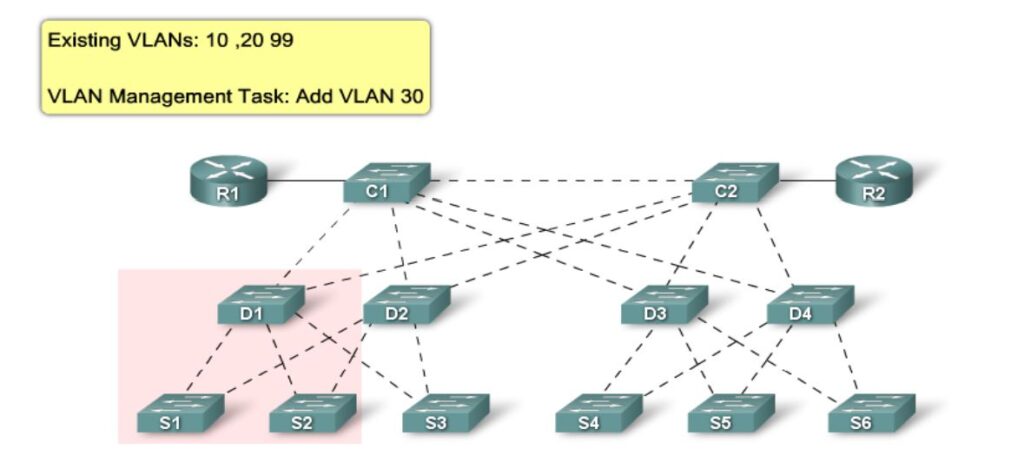
VTP allows a network manager to configure a switch so that it will propagate VLAN configurations to other switches in the network. The switch can be configured in the role of a VTP server or a VTP client. VTP only learns about normal-range VLANs (VLAN IDs 1 to 1005). Extended-range VLANs (IDs greater than 1005) are not supported by VTP.
VTP benefits:
- VLAN configuration consistency across the network
- Accurate tracking and monitoring of VLANs
- Dynamic reporting of added VLANs across a network
- Dynamic trunk configuration when VLANs are added to the network
The VTP Protocol:
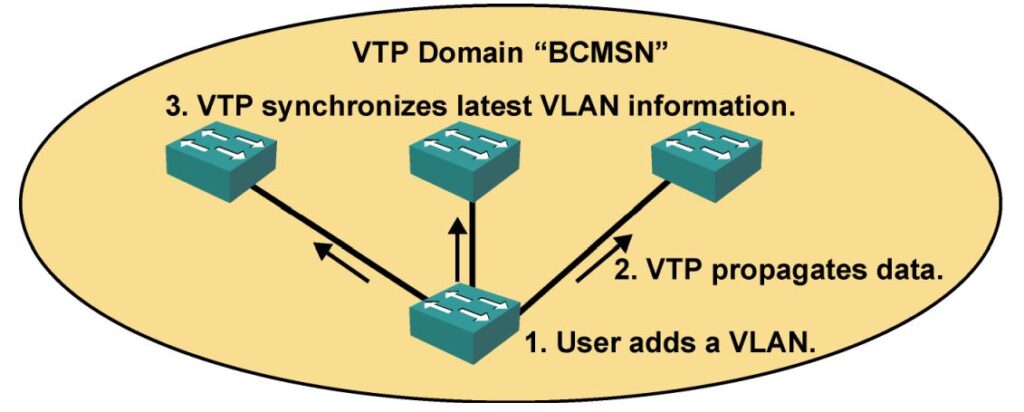
- Advertises VLAN configuration information
- Maintains VLAN configuration consistency throughout a common
- Administrative domain
- Sends advertisements on trunk ports only
VTP Configuration:
Switch(config)#vtp domain name Switch(config)#vtp mode mode Switch(config)#vtp password password
To verify the VTP Config:
Switch(config)#show vtp status VTP Version : 2 Configuration Revision : 28 Maximum VLANs supported locally : 1005 Number of existing VLANs : 17 VTP Operating Mode : Client VTP Domain Name : BCMSN VTP Pruning Mode : Enabled VTP V2 Mode : Disabled VTP Traps Generation : Disabled MD5 digest : 0x45 0x52 0xB6 0xFD 0x63 0xC8 0x49 0x80 Configuration last modified by 10.1.1.1 at 8-12-05 15:04:49 Switch(config)#show vtp counters
Need expert help with this in production?
Youngster Company offers hands-on services for the topics covered on this blog — cybersecurity audits (ISO 27001 / IT compliance), penetration testing, DevOps automation, server & network configuration, and digital forensics / OSINT investigations. If you need this implemented, audited, or troubleshot for your business, get in touch.
