AAA (Authentication, authorization, and accounting )
- Authentication provides a method to identify the users. The user is first identified before access is allowed.
- Authorization describes what a user is allowed to perform.
- Accounting provides a method that allows users to identify what resources of the network are accessed and for how long. This information can be used later for billing, for example.
- AAA uses some protocols to manage its security functions. Among others, a couple of them are very common: RADIUS and TACACS.
Radius:
Remote Authentication Dial-In User Service (RADIUS) is a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA or Triple A) management for users who connect and use a network service.
TACACS+
Terminal Access Controller Access-Control System Plus (TACACS+) is a protocol developed by Cisco and released as an open standard beginning in 1993. Although derived from TACACS, TACACS+ is a separate protocol that handles authentication, authorization, and accounting (AAA) services.
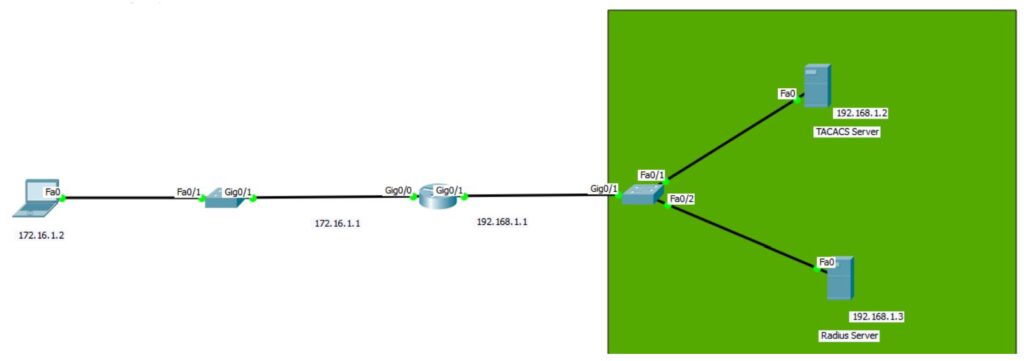
AAA Configuration:
Router(config)#aaa new-model Router(config)#tacacs-server host 192.168.1.2 key cisco123 Router(config)#radius-server host 192.168.1.3 auth-port 1645 key cisco123 Router(config)#aaa authentication login My_Rules group tacacs+ group radius local Router(config)#username Youngster secret ccie Router(config)#line vty 0 4 Router(config-line)#login authentication My_Rules
Need expert help with this in production?
Youngster Company offers hands-on services for the topics covered on this blog — cybersecurity audits (ISO 27001 / IT compliance), penetration testing, DevOps automation, server & network configuration, and digital forensics / OSINT investigations. If you need this implemented, audited, or troubleshot for your business, get in touch.
